This guide covers the part we actually validated on a live Ubuntu server: installation, shell path setup, onboarding, gateway service creation, and the checks you should run before you move on to Telegram or email.
What This Guide Covers
By the end of this tutorial, you should have:
- OpenClaw installed and callable from your shell
- a supported Node runtime available for OpenClaw
- onboarding completed far enough to install the user-level gateway service
- the gateway reachable through the local control UI
This guide intentionally stops there. Telegram and email channel setup should come only after the gateway is stable.
Prerequisites
Before you start, you need:
- an Ubuntu server or Linux machine you control
- a shell user with install permissions
- an OpenAI API key if you plan to use OpenAI during onboarding
- internet access from the server
- SSH access and enough disk space to install Node and OpenClaw
Step 1: Install OpenClaw
Start with the standard npm install path:
npm install -g openclaw@latestOn a machine that already has a supported Node version, this is the most direct install path.
If the npm install fails, switch to this fallback immediately:curl -fsSL https://openclaw.ai/install-cli.sh | bashUse the fallback installer especially when the host is still on an older Node version and npm install cannot satisfy OpenClaw’s runtime requirements. On the validated Ubuntu server, the fallback installer reported:
- Node
22.22.0installed in user space - OpenClaw
2026.4.15installed successfully
Time estimate: 3 to 6 minutes, depending on package download speed.

Step 2: Verify the CLI and Node Runtime
After install, verify that the shell can see
openclaw
and the correct Node runtime:
which openclaw
openclaw --version
which node
node -vIf the installer script was used and the current shell did not pick up the new binaries automatically, export the paths explicitly:
export PATH="$HOME/.openclaw/bin:$HOME/.openclaw/tools/node-v22.22.0/bin:$PATH"
hash -rThen run the same checks again. You want to see:
openclawresolving from a valid install pathnodereporting a supported 22+ version
If that works, make it persistent:
echo 'export PATH="$HOME/.openclaw/bin:$HOME/.openclaw/tools/node-v22.22.0/bin:$PATH"' >> ~/.bashrc
source ~/.bashrcTime estimate: 2 to 4 minutes.
Step 3: Start Onboarding

Once the CLI and Node path are correct, begin onboarding:
openclaw onboard --install-daemonDuring onboarding, OpenClaw will walk you through provider setup, workspace creation, and gateway service installation. On the validated run, the service install stage reported:
Installed systemd service: /home/ubuntu/.config/systemd/user/openclaw-gateway.serviceThis means the gateway is installed as a
user-level systemd service. If you are using OpenAI during onboarding, provide the OpenAI API key when prompted. Time estimate: 5 to 10 minutes, depending on how quickly you answer the interactive prompts.

Step 4: Verify the Gateway Service Exists
After onboarding reaches the service install stage, verify that the user service file exists:
ls -la ~/.config/systemd/user/openclaw-gateway.serviceYou can also inspect it directly:
cat ~/.config/systemd/user/openclaw-gateway.serviceThis lets you confirm:
- the service file was written
- it is running as your Unix user
- the command path matches the installed OpenClaw binary
Time estimate: 1 to 2 minutes.
Step 5: Bring the Gateway Up
Once the service exists, reload user systemd and restart the gateway:
systemctl --user daemon-reload
systemctl --user restart openclaw-gatewayThen check status:
systemctl --user status openclaw-gateway --no-pager -lOpenClaw also exposes gateway and control UI checks through its CLI:
openclaw status
openclaw health --jsonThe local control UI should be available at:
http://127.0.0.1:18789/If onboarding prints a tokenized control UI URL, keep it. That is useful for immediate validation. Time estimate: 2 to 5 minutes.
Step 6: If the Gateway Fails Health Checks
On the validated setup, onboarding reached a point where the control UI was exposed but the health check still reported:
gateway closed (1006)That is the point where you stop pushing forward into Telegram or email setup. Debug the gateway first. Use these commands:
systemctl --user status openclaw-gateway --no-pager -l
journalctl --user -u openclaw-gateway -n 100 --no-pager
cat ~/.config/systemd/user/openclaw-gateway.serviceWhat you are looking for:
- a bad executable path in the user service
- a shell PATH mismatch between your login shell and the systemd user service
- a crash on startup
- a port bind failure on
127.0.0.1:18789
Do not continue with Telegram or Gmail until
openclaw health --json
reports a healthy gateway.
How Long Does This Part Take?
If everything goes smoothly:
- install: 3 to 6 minutes
- CLI and Node verification: 2 to 4 minutes
- interactive onboarding: 5 to 10 minutes
- gateway service verification: 2 to 5 minutes
A realistic total for install, onboarding, and gateway bring-up is about 12 to 25 minutes for a technical user.
Where to Go Next
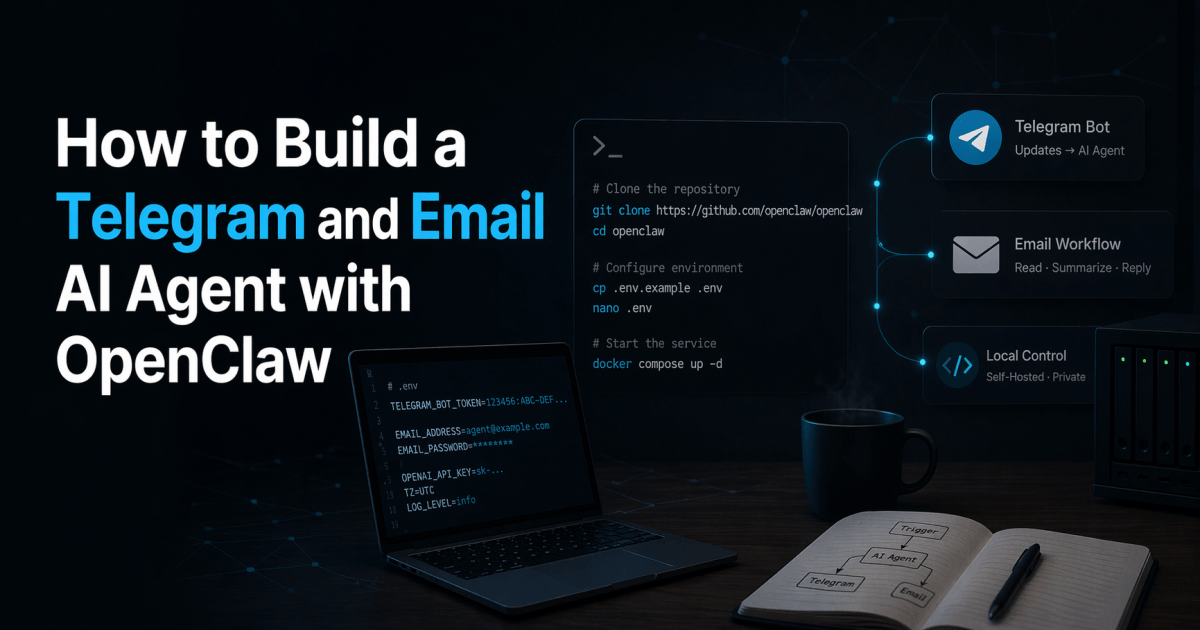
Once the gateway is healthy, the next phase is channel setup:
- Telegram bot creation and pairing
- Gmail watch, Pub/Sub, and webhook delivery if you want email in the loop
Those steps should be treated as a second phase, not bundled into the first bootstrapping session.
Related Reading
- How to Build a Telegram and Email AI Agent with Brainybear
- Which Is Faster for Building a Telegram and Email AI Agent OpenClaw or Brainybear
This draft reflects the OpenClaw install and onboarding path validated through CLI install, fallback installer usage, user-level systemd service creation, and gateway health-check troubleshooting.